analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
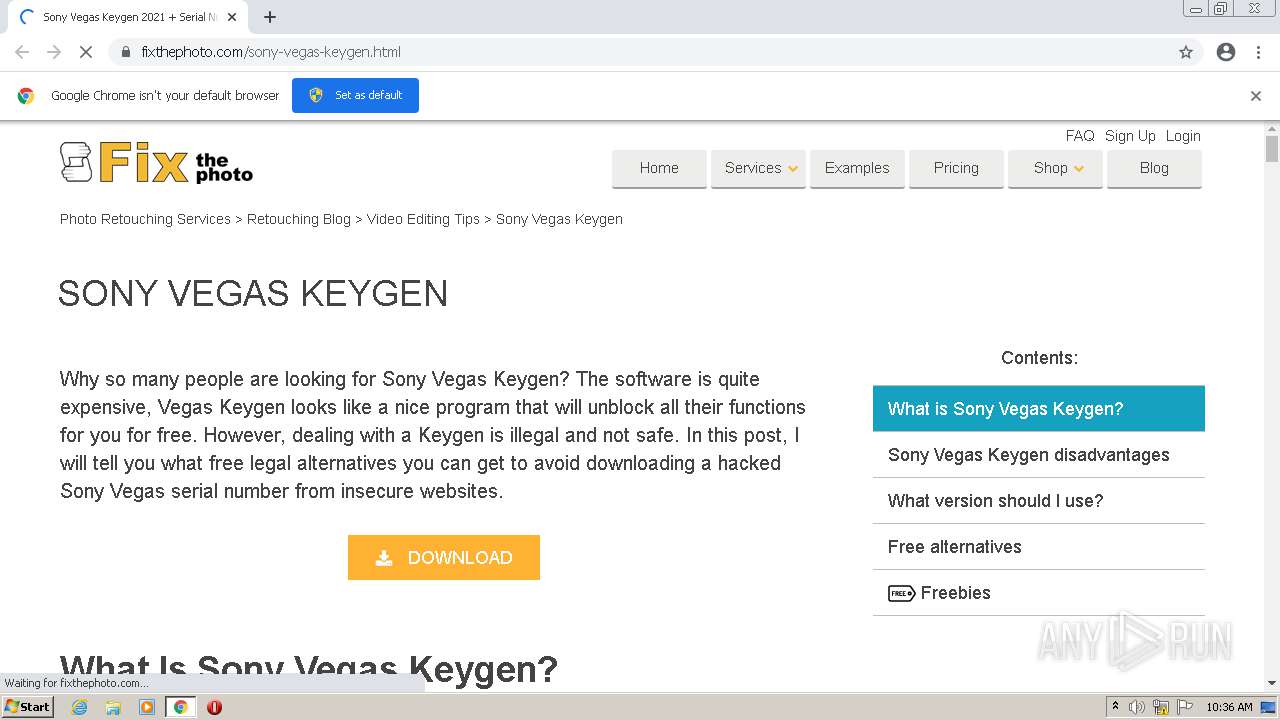
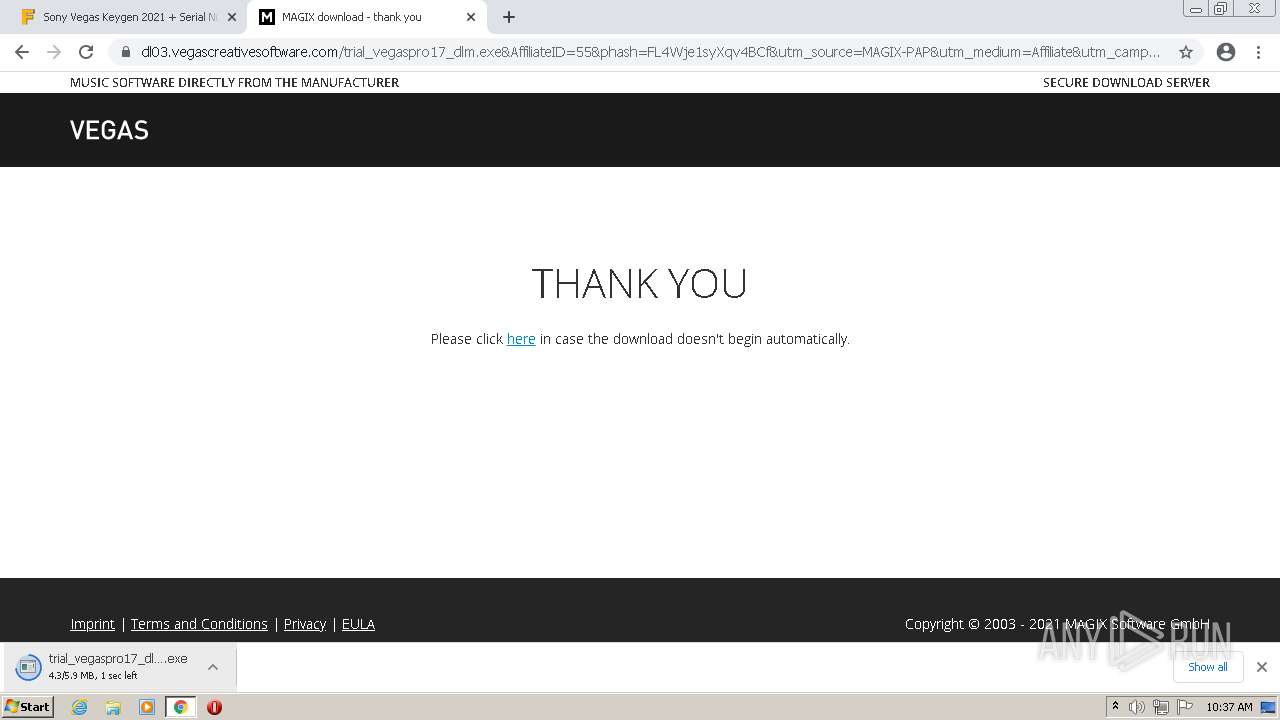
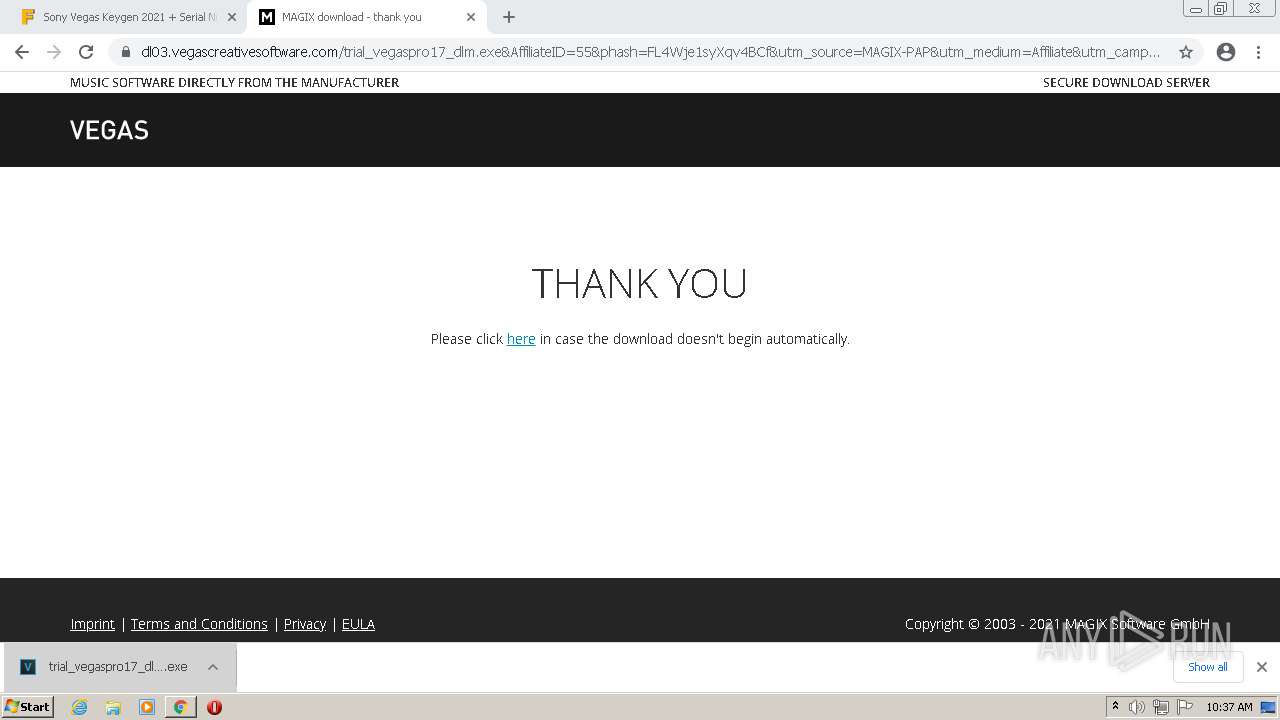
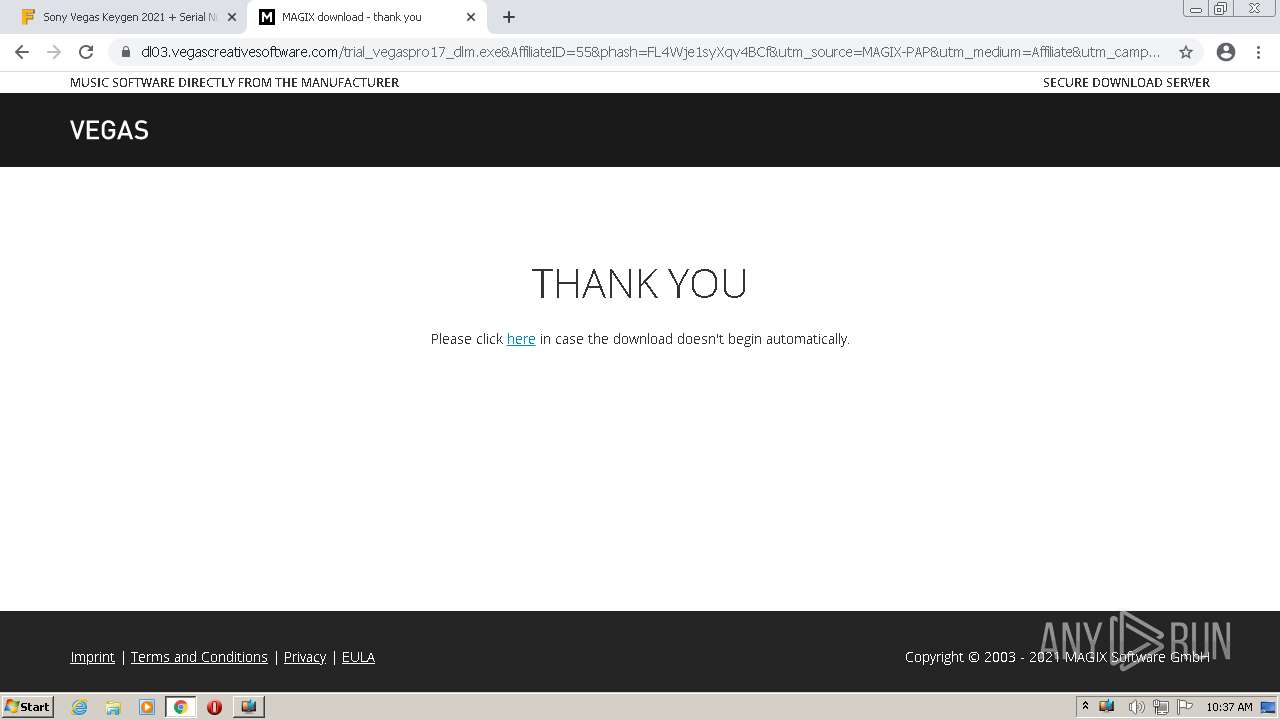
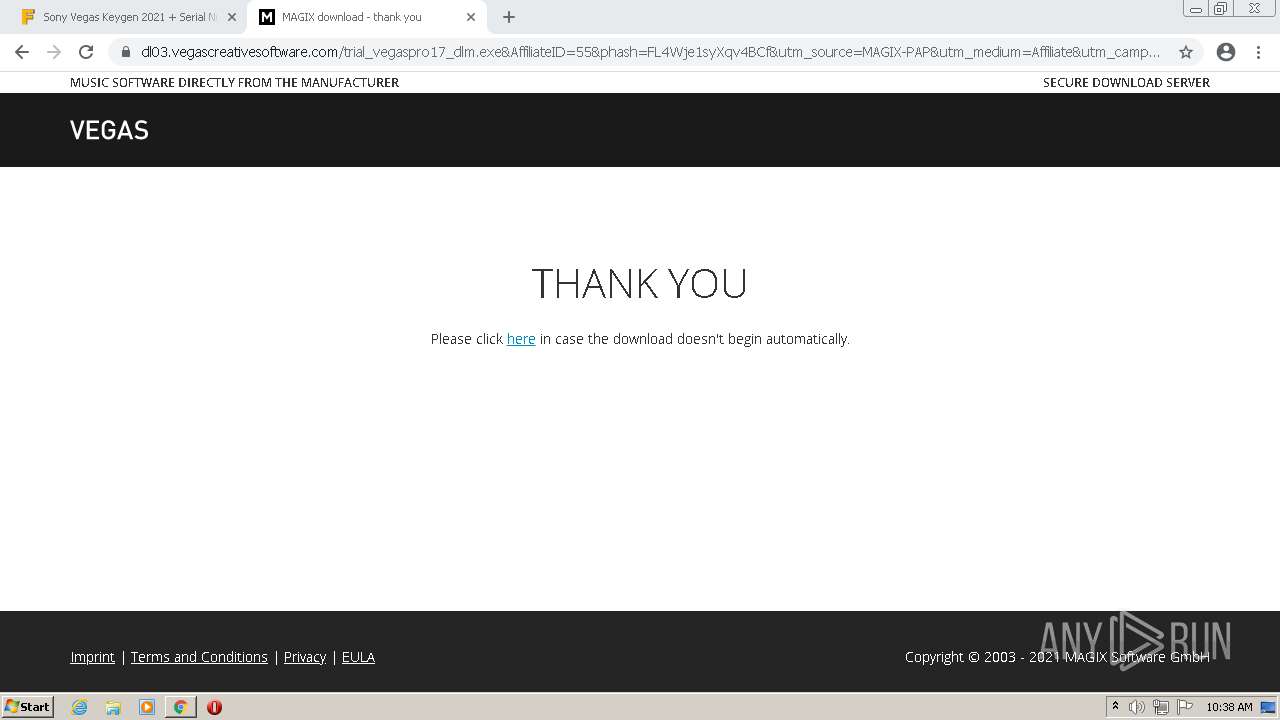
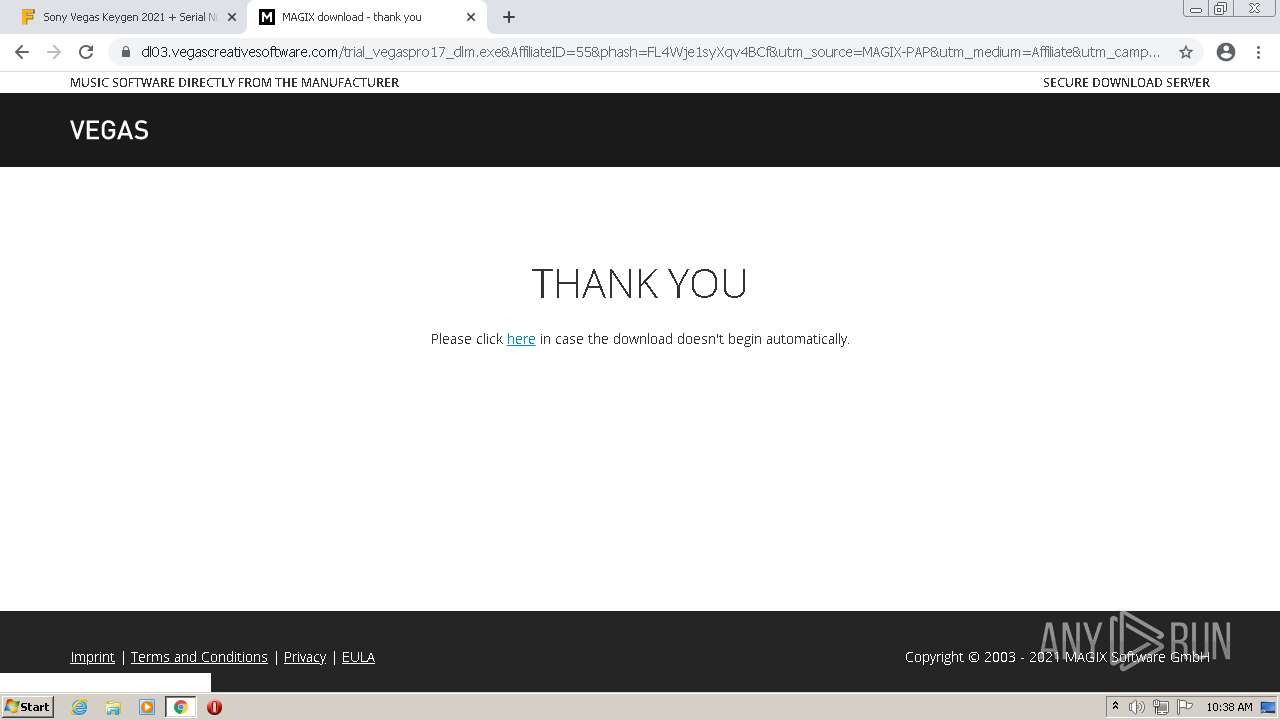
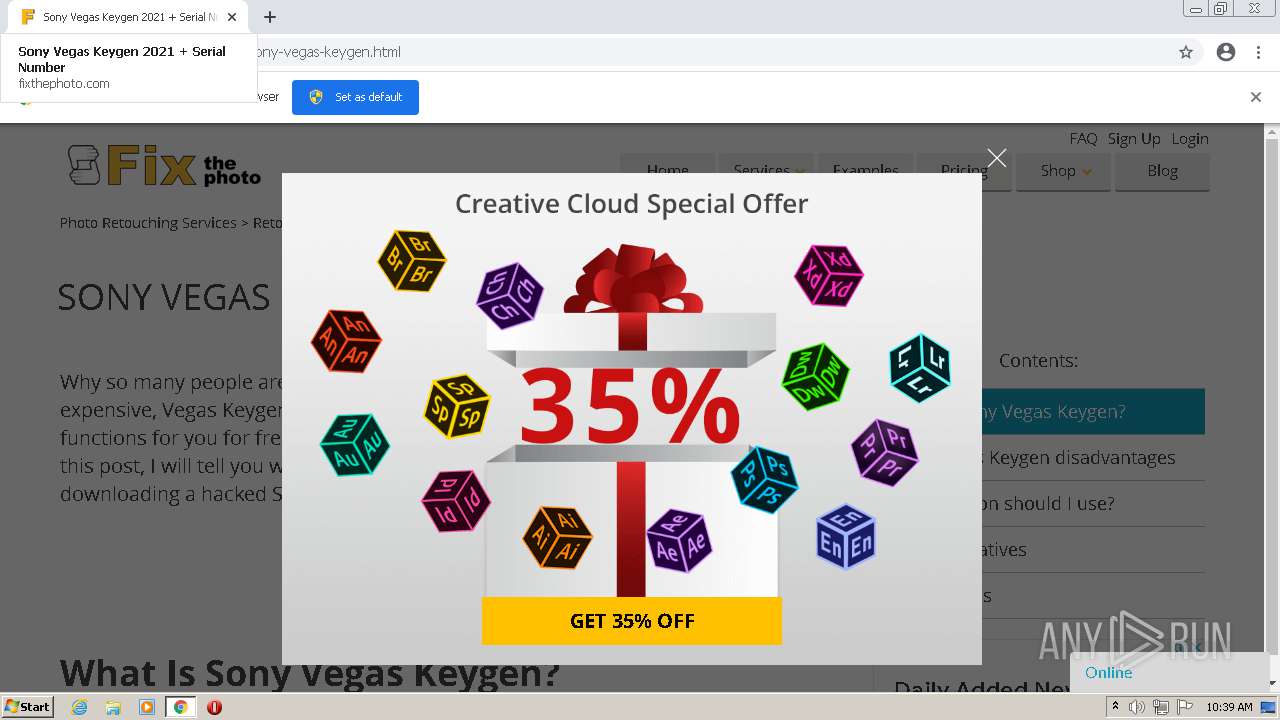
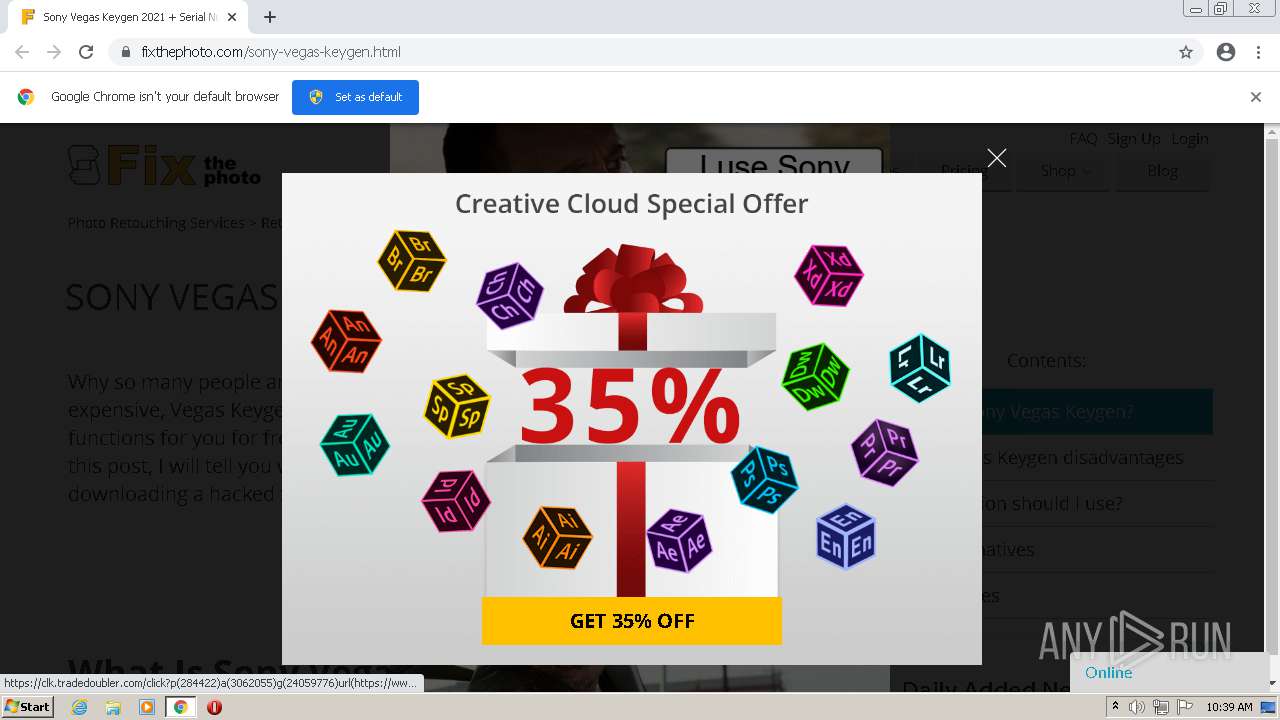
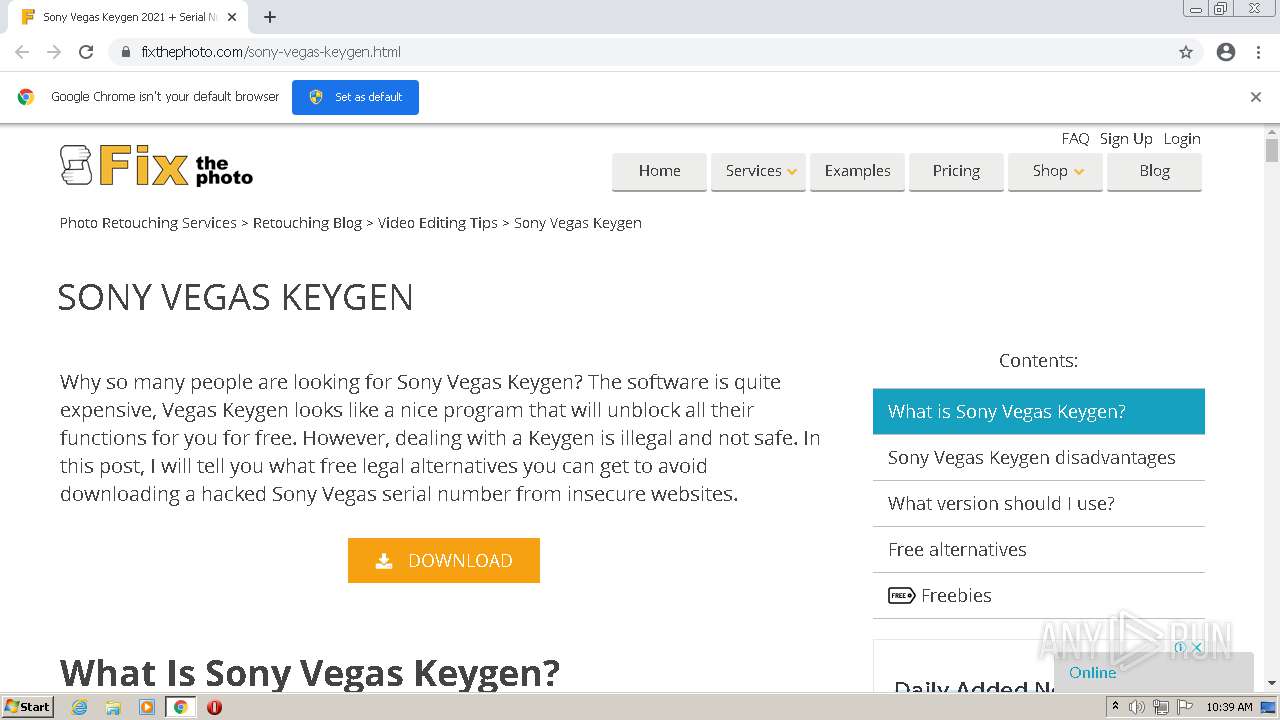
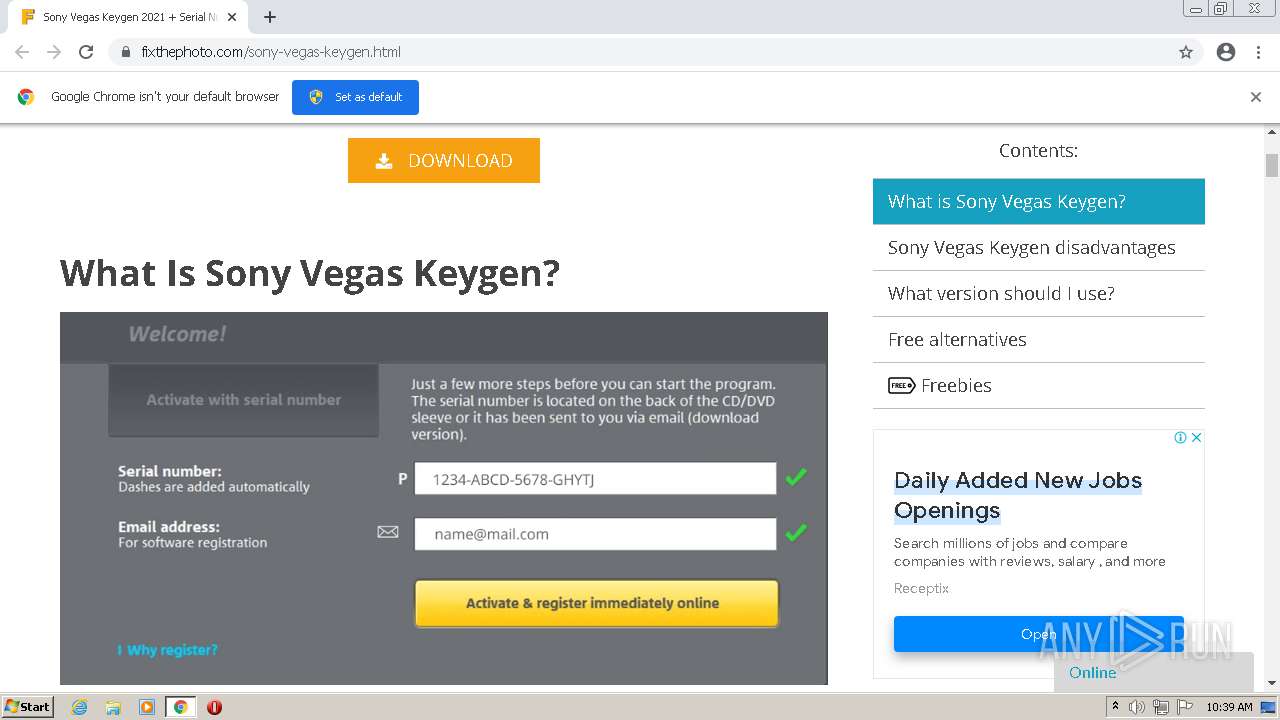
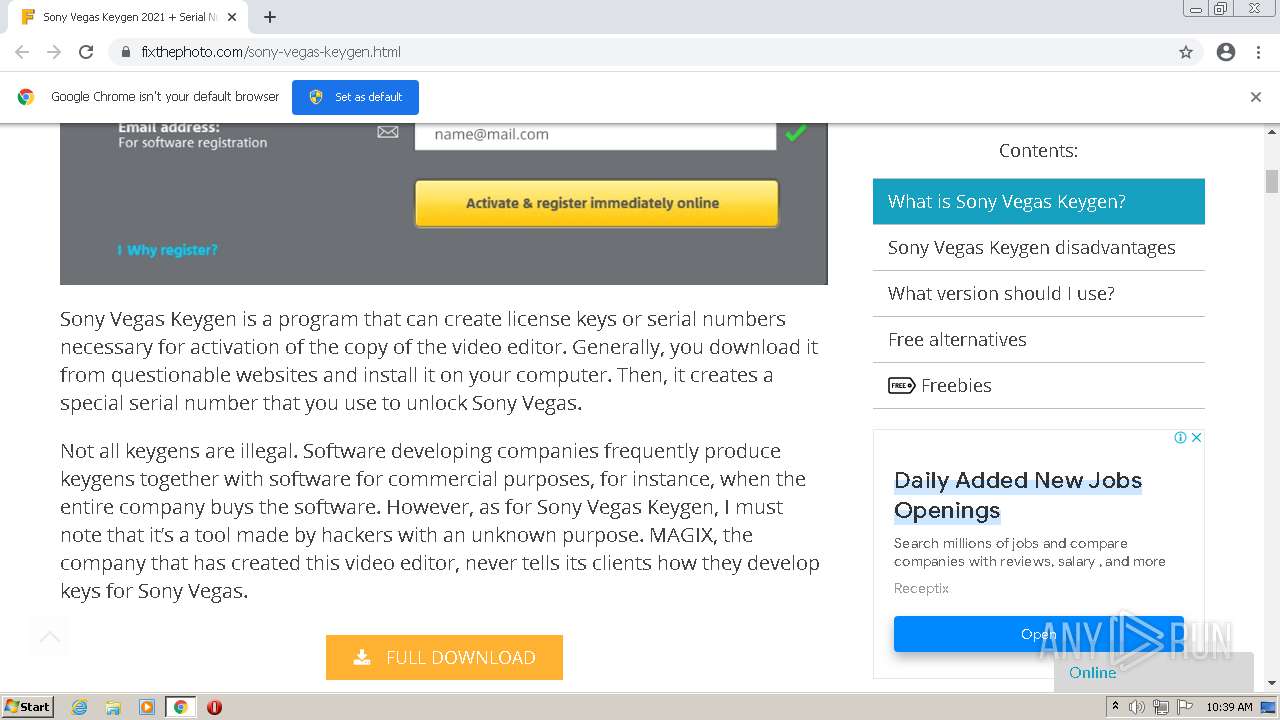
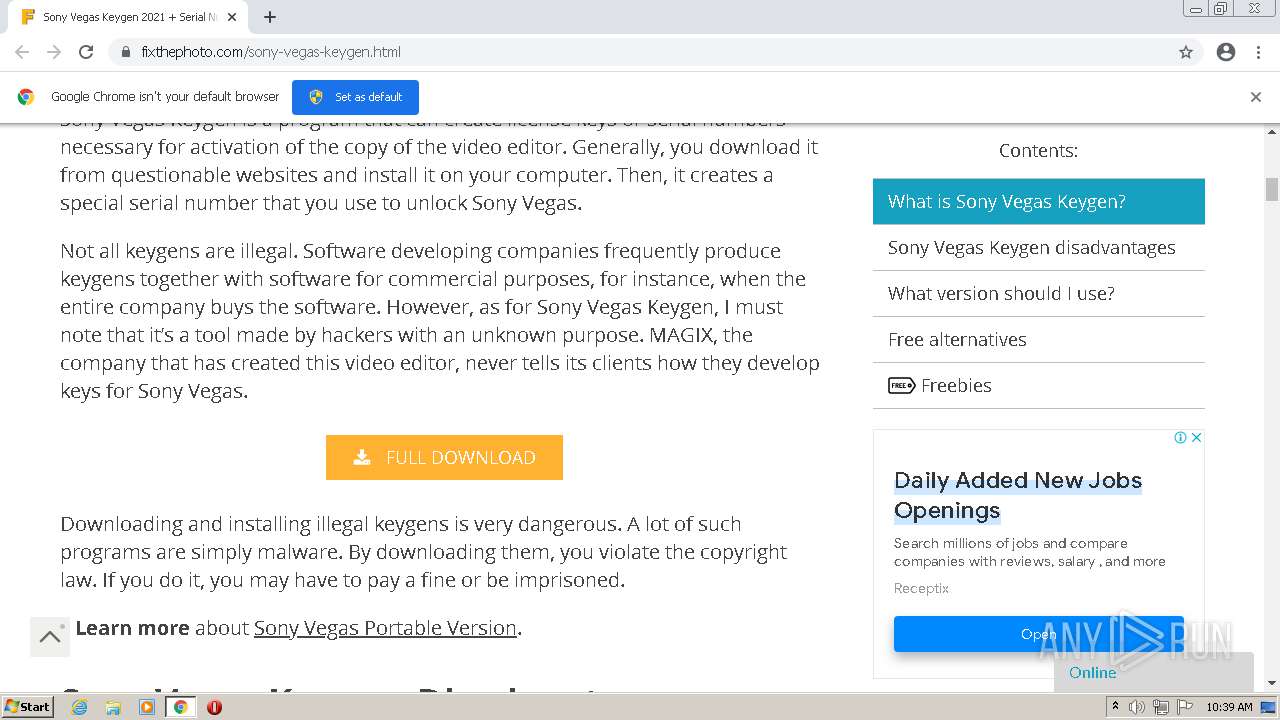
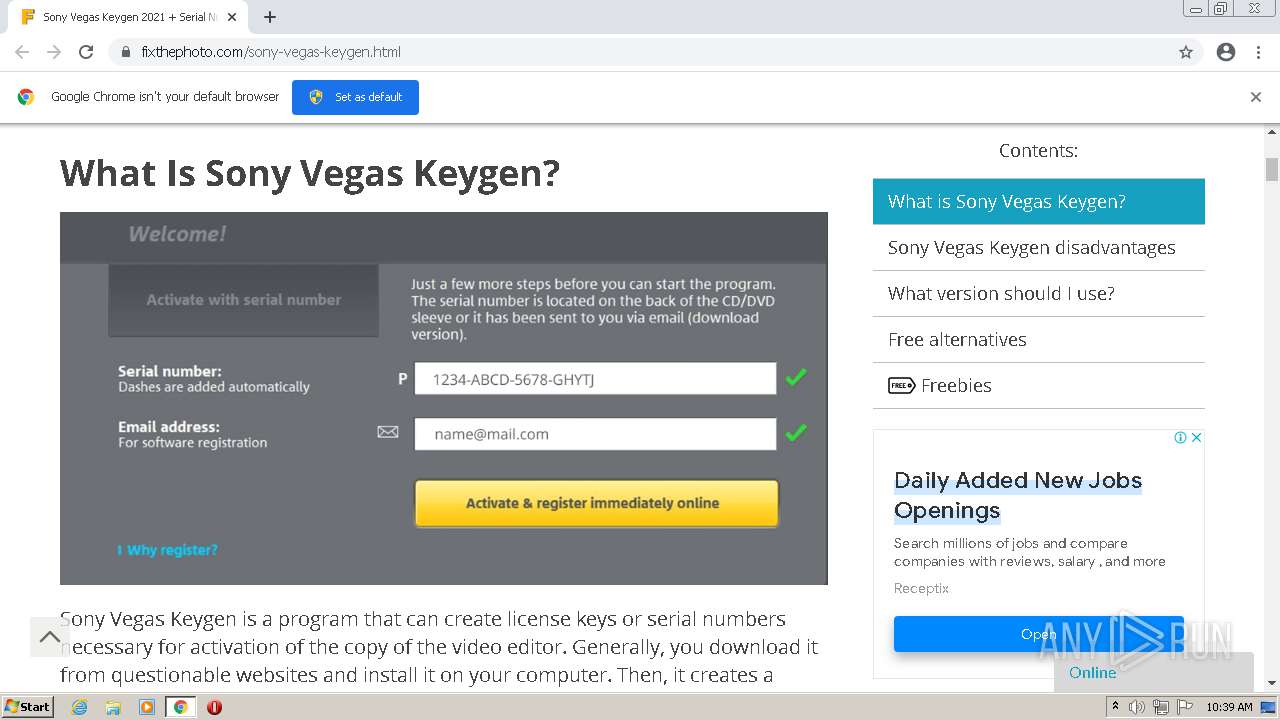
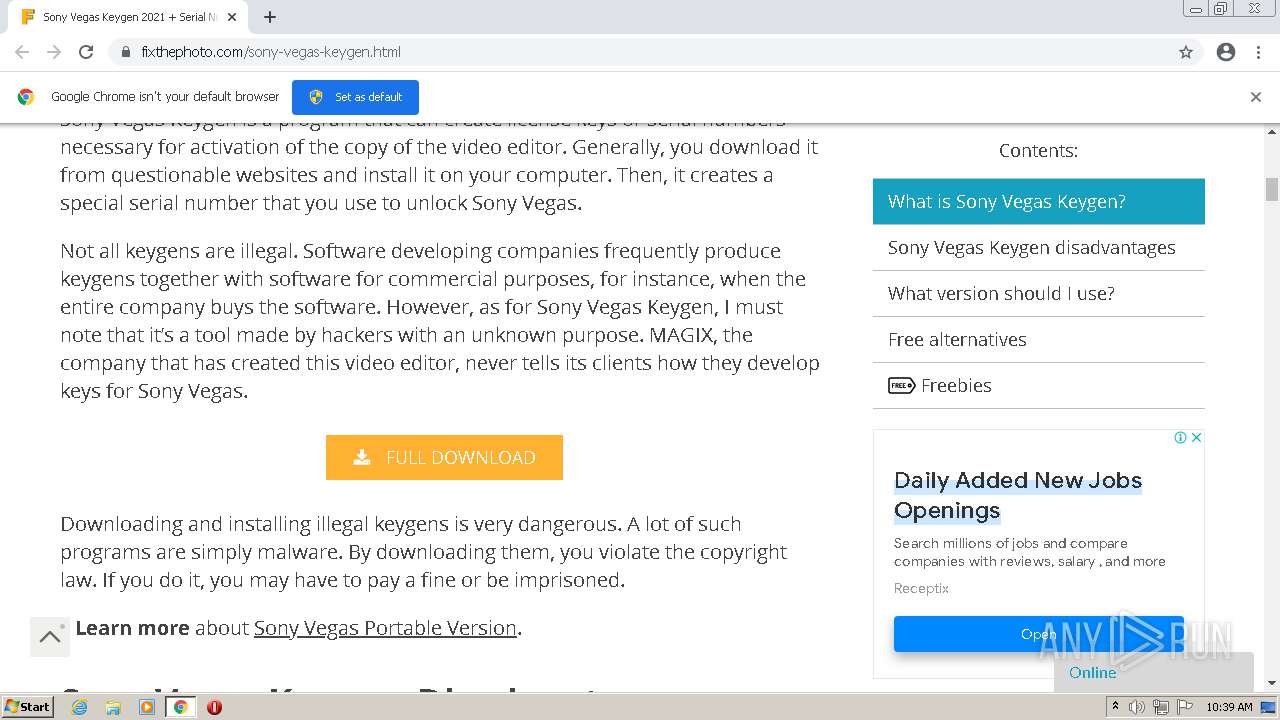
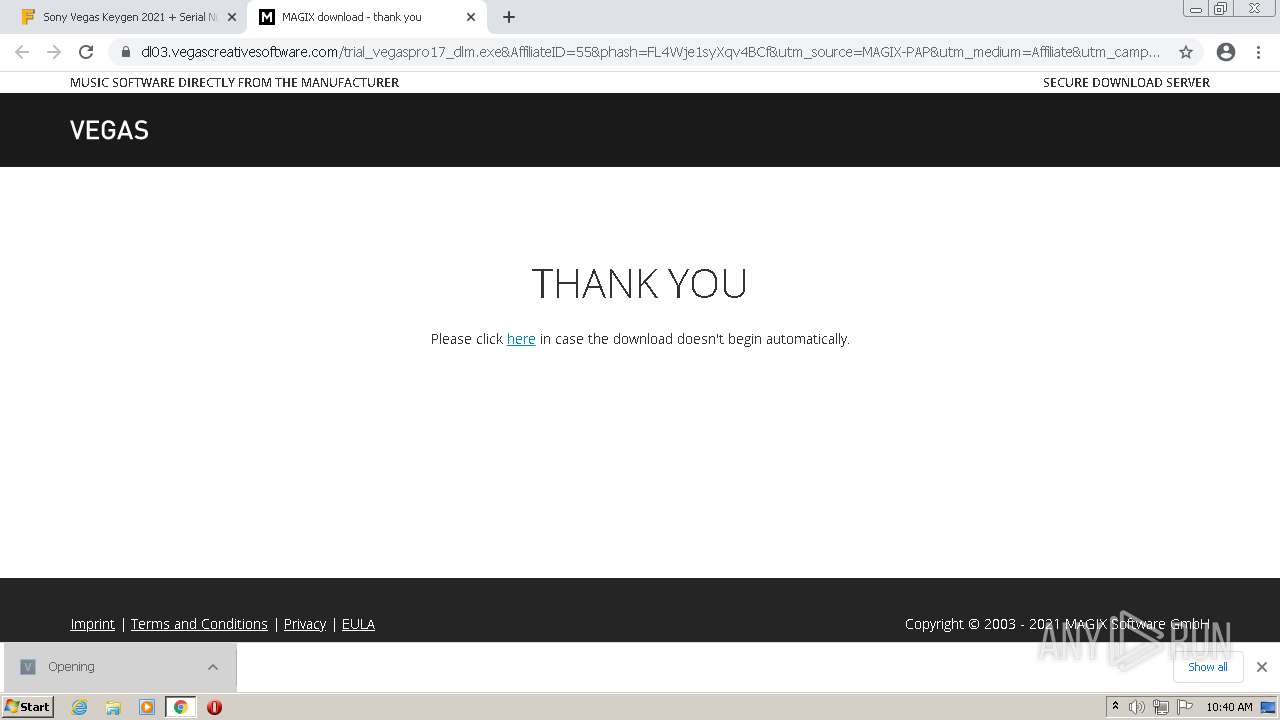
| URL: | https://fixthephoto.com/sony-vegas-keygen.html |
| Full analysis: | https://app.any.run/tasks/409a8850-c892-4421-aa51-586e6c6b5c20 |
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2021, 09:35:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 664B5D53C5F5F8A3C644646BC88CFAF3 |
| SHA1: | 9E240AF8C1A800CDE5B1DAC5A0E219452181EC7D |
| SHA256: | 5D74E509868E37B5518A8493486D65434A8791B22E36DA53558A95B55C19B755 |
| SSDEEP: | 3:N8fnRDBxLQn:2fl8n |
MALICIOUS
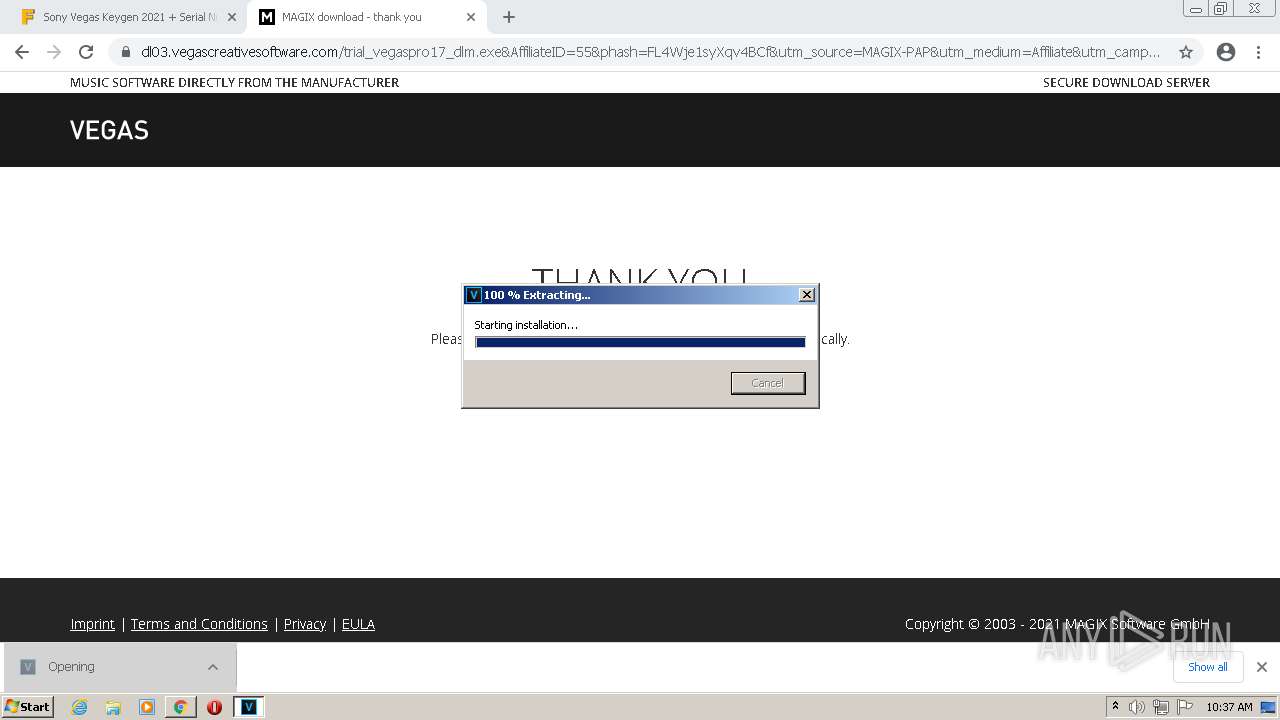
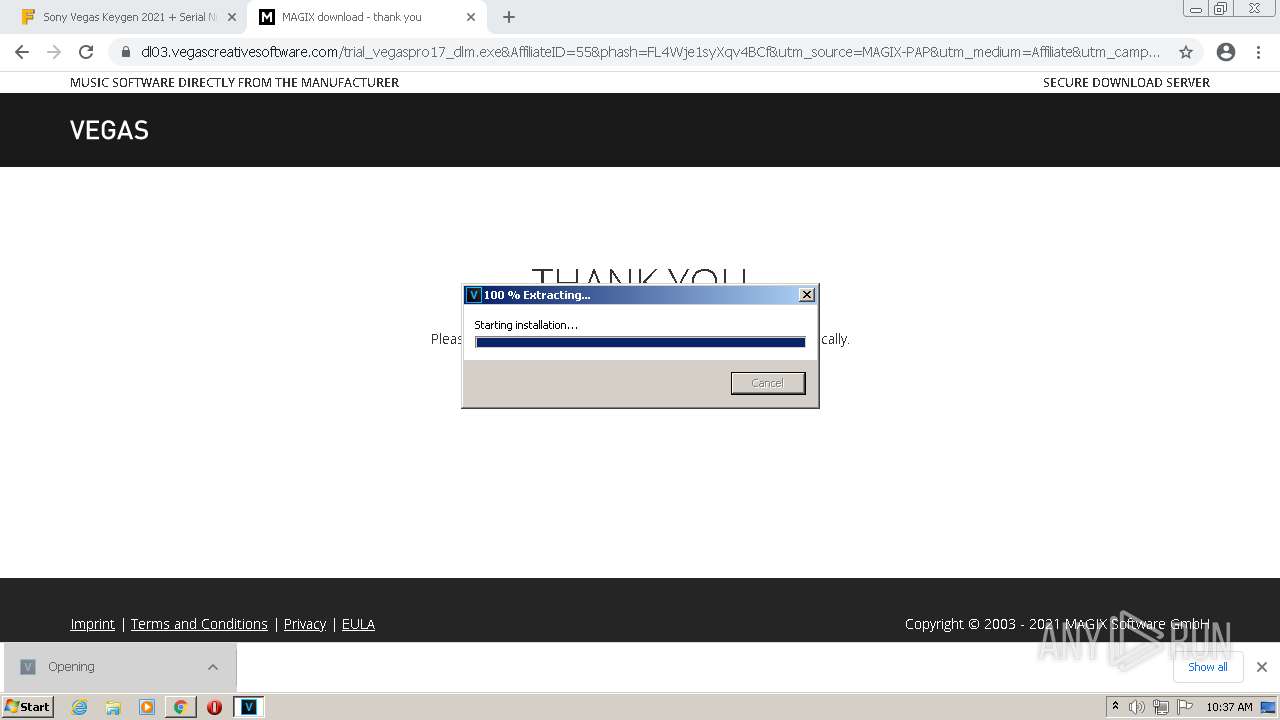
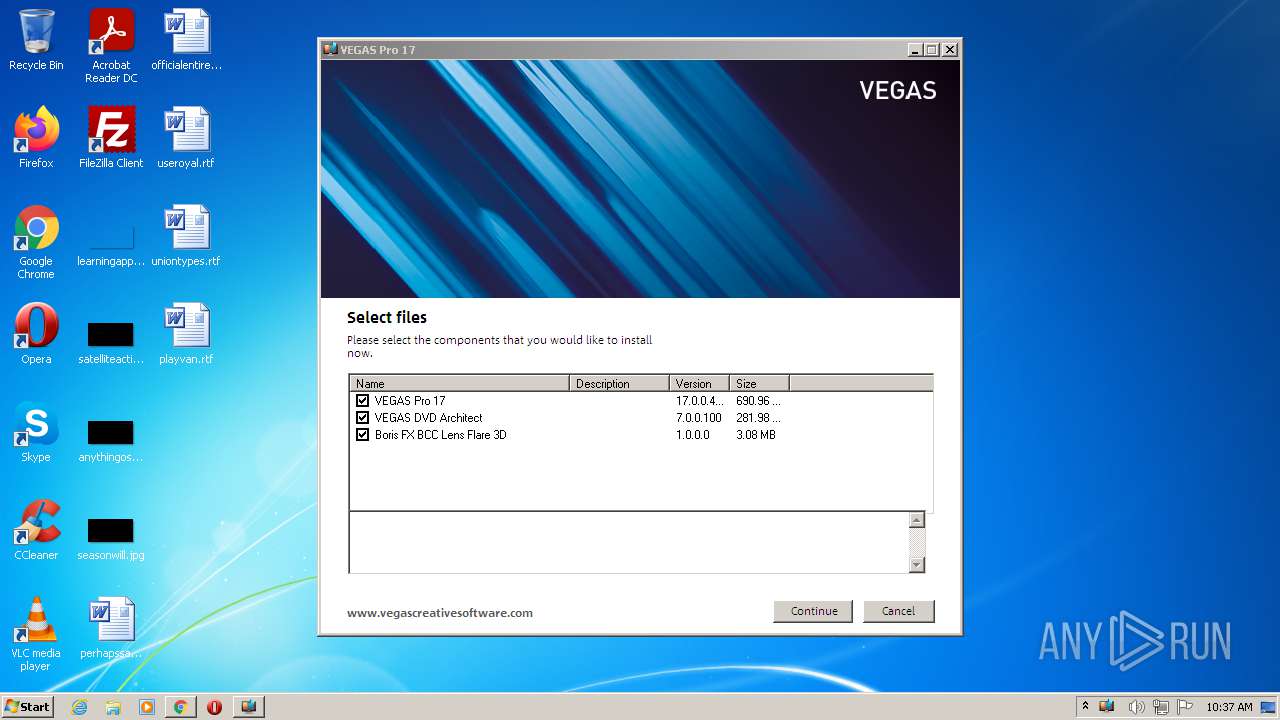
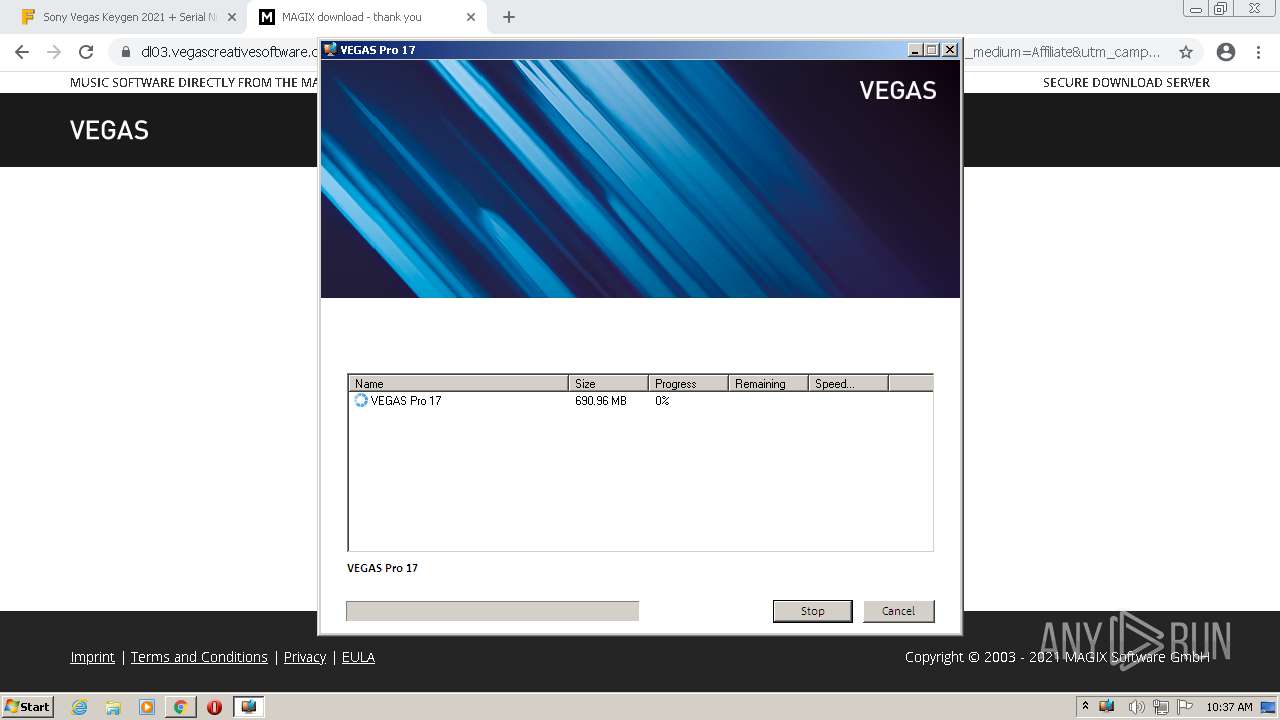
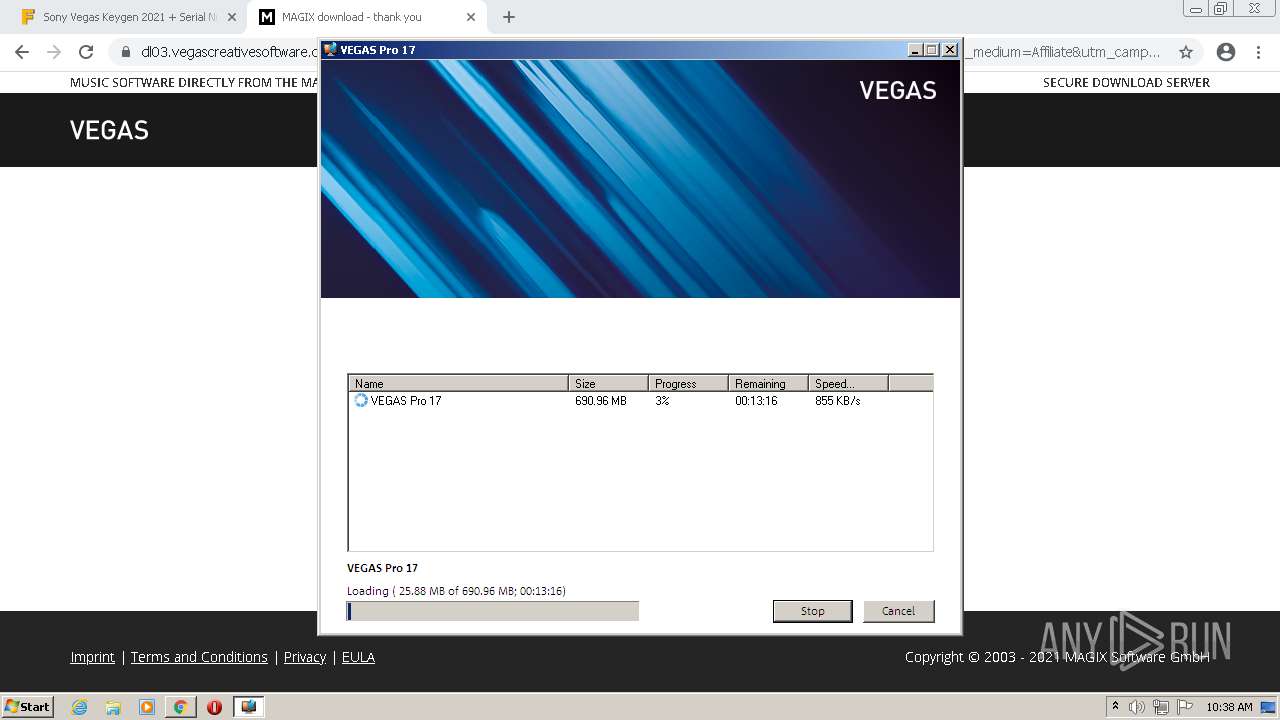
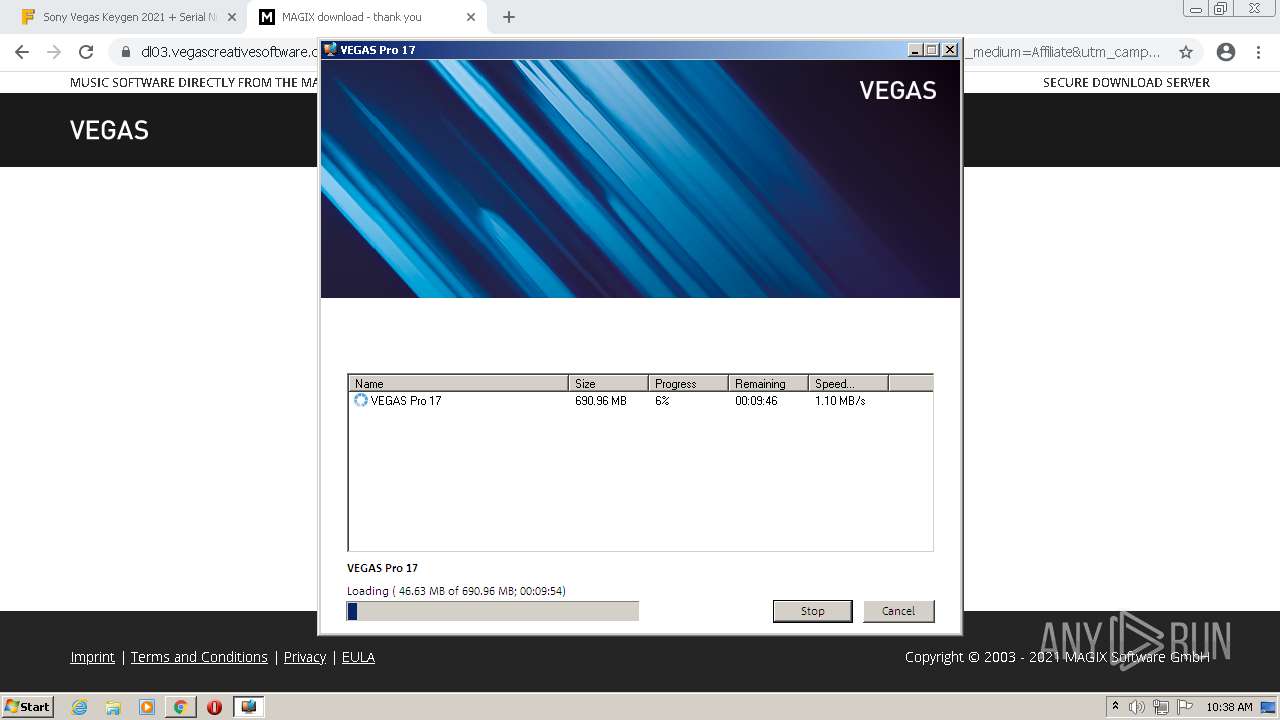
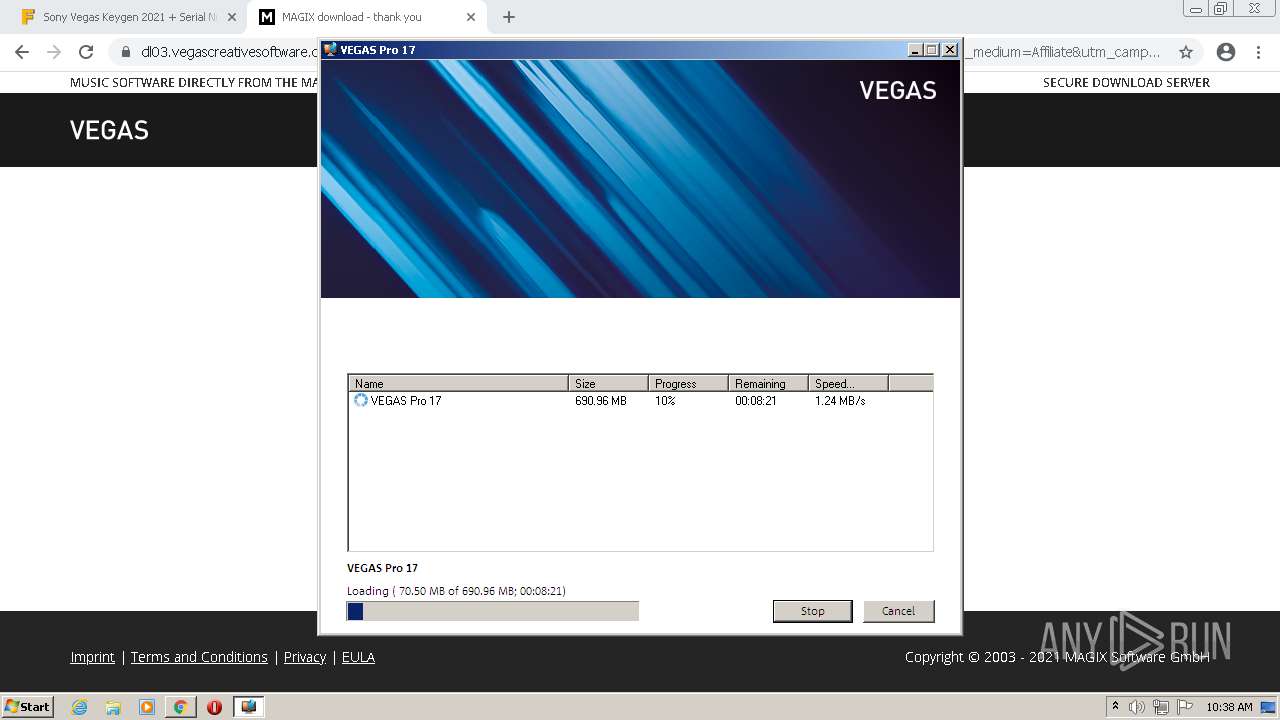
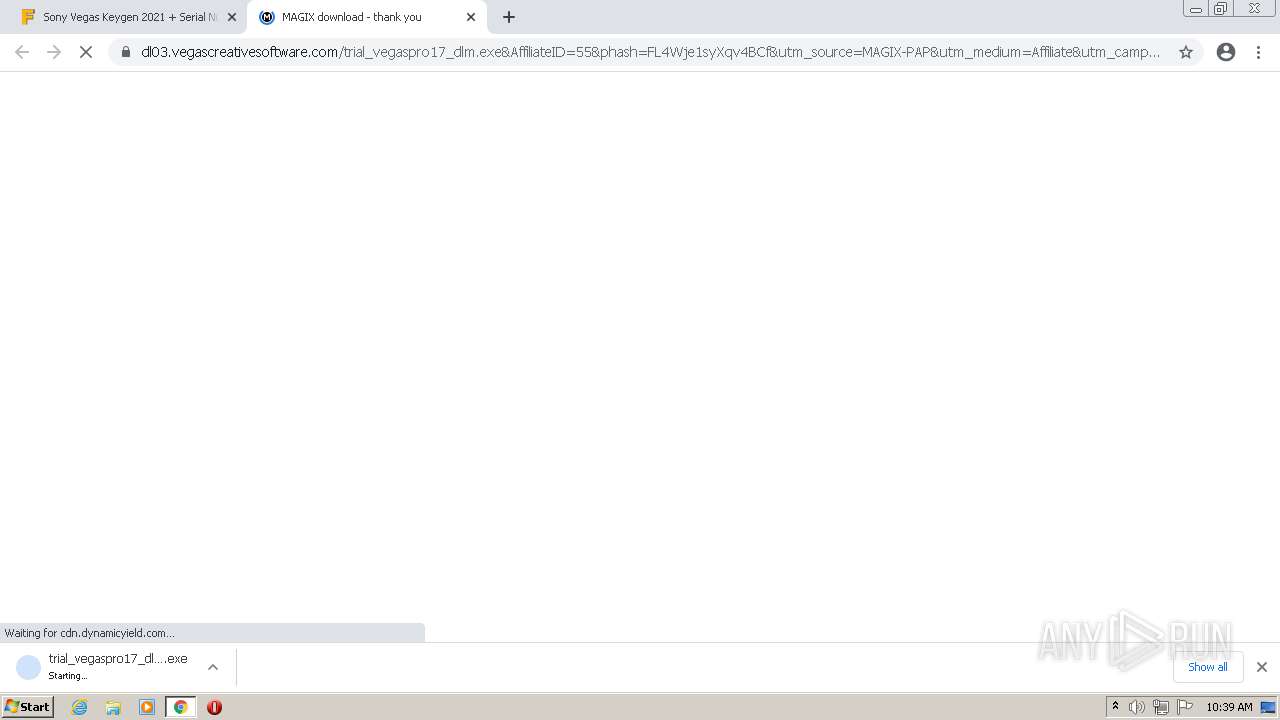
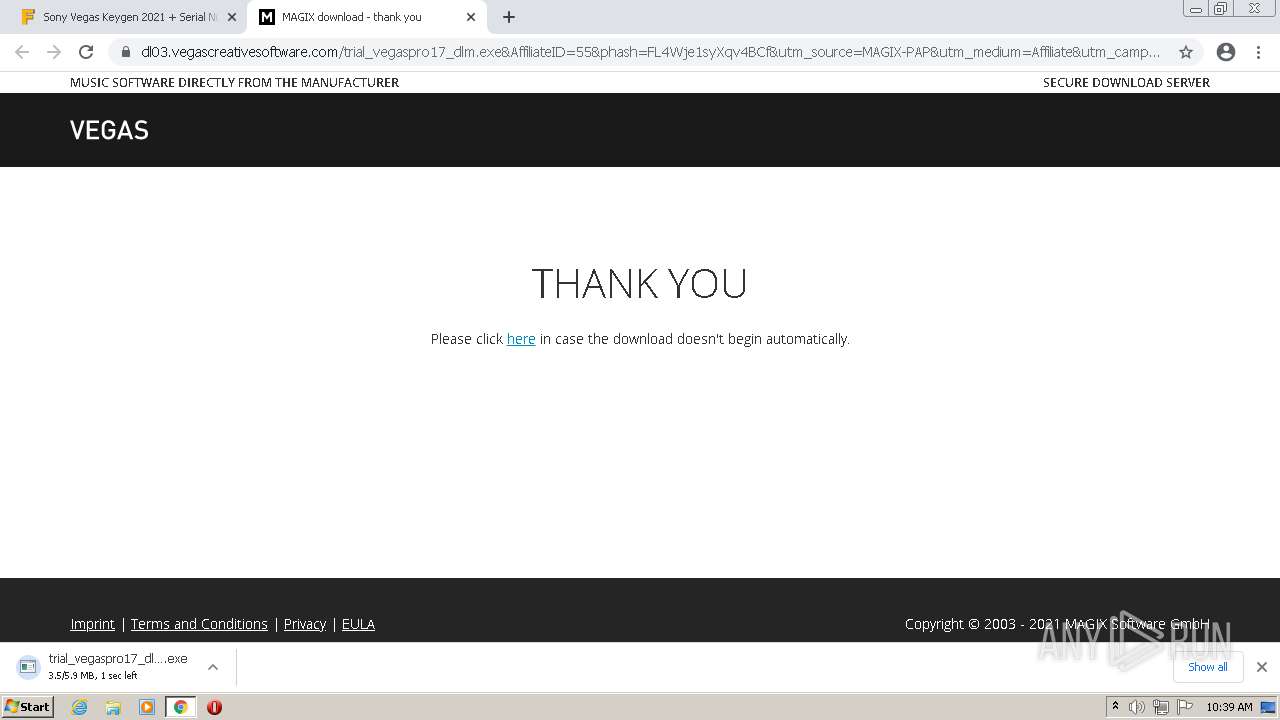
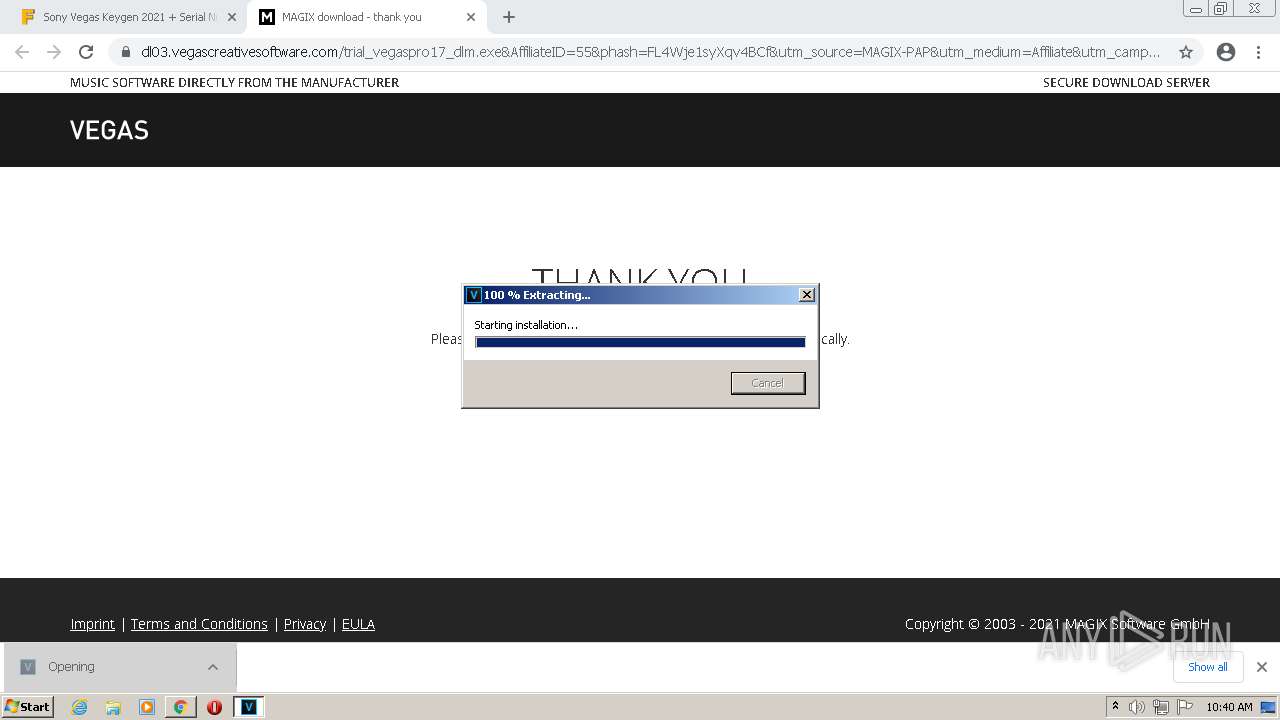
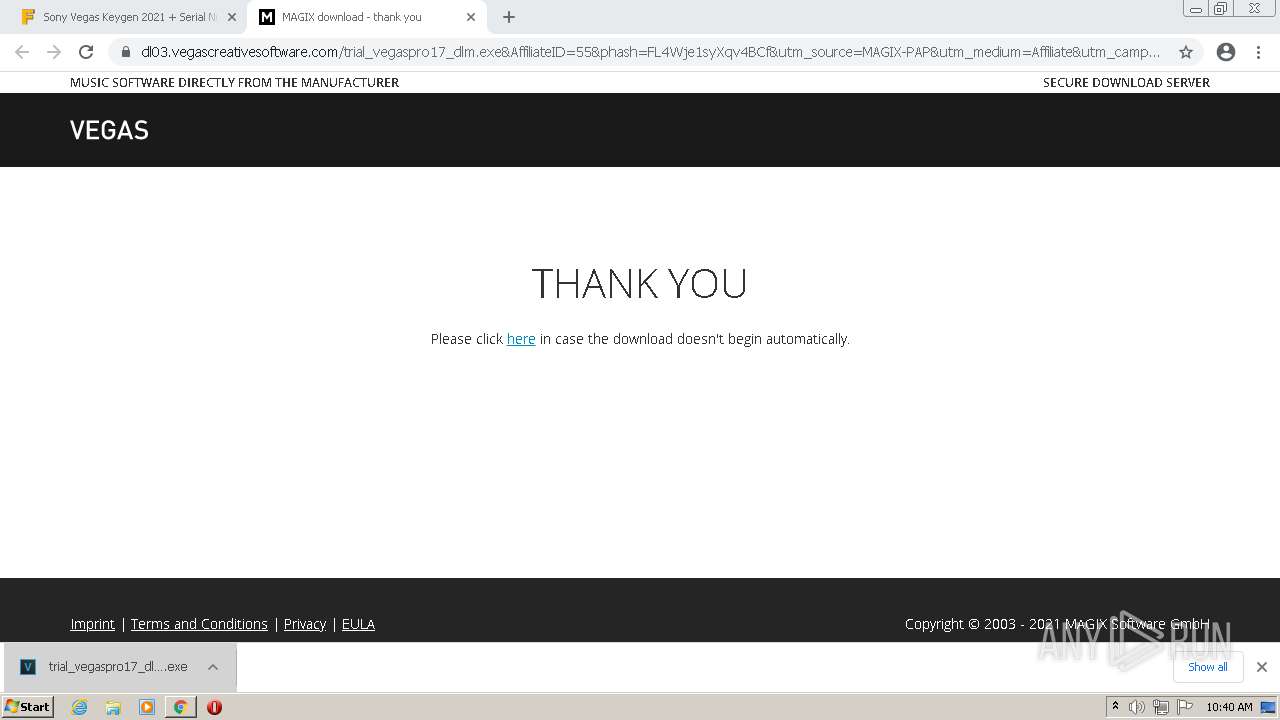
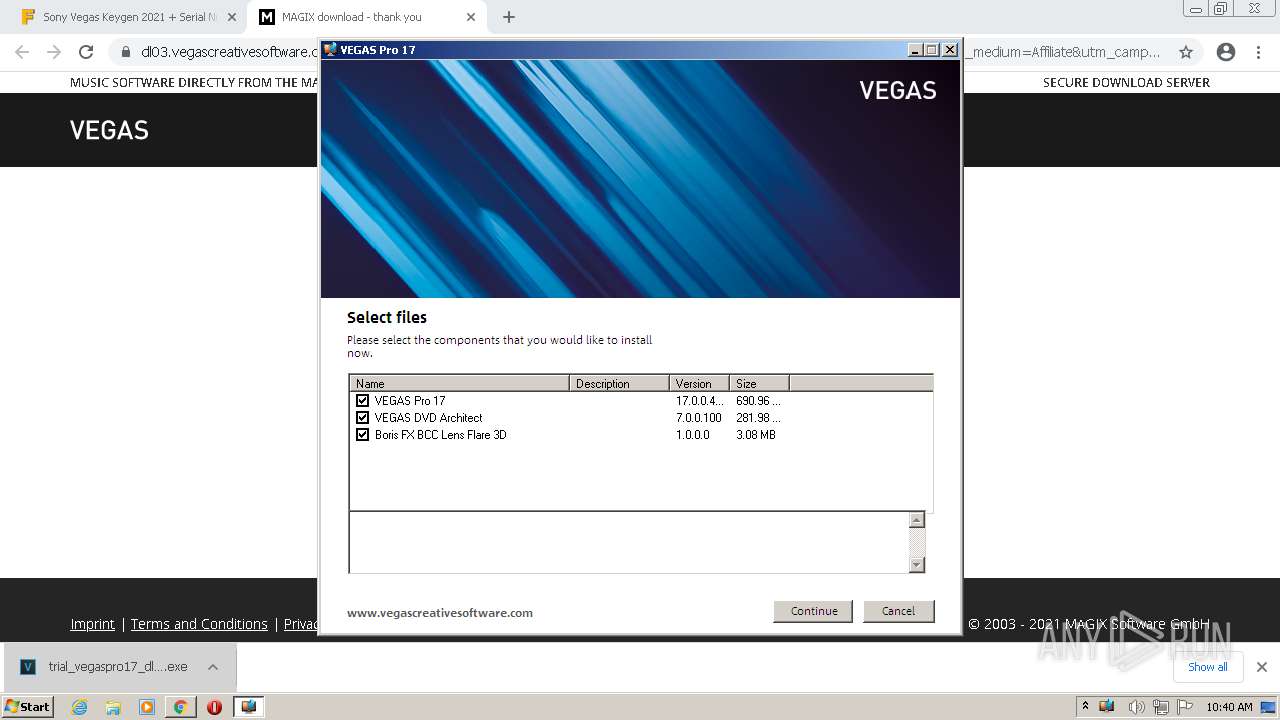
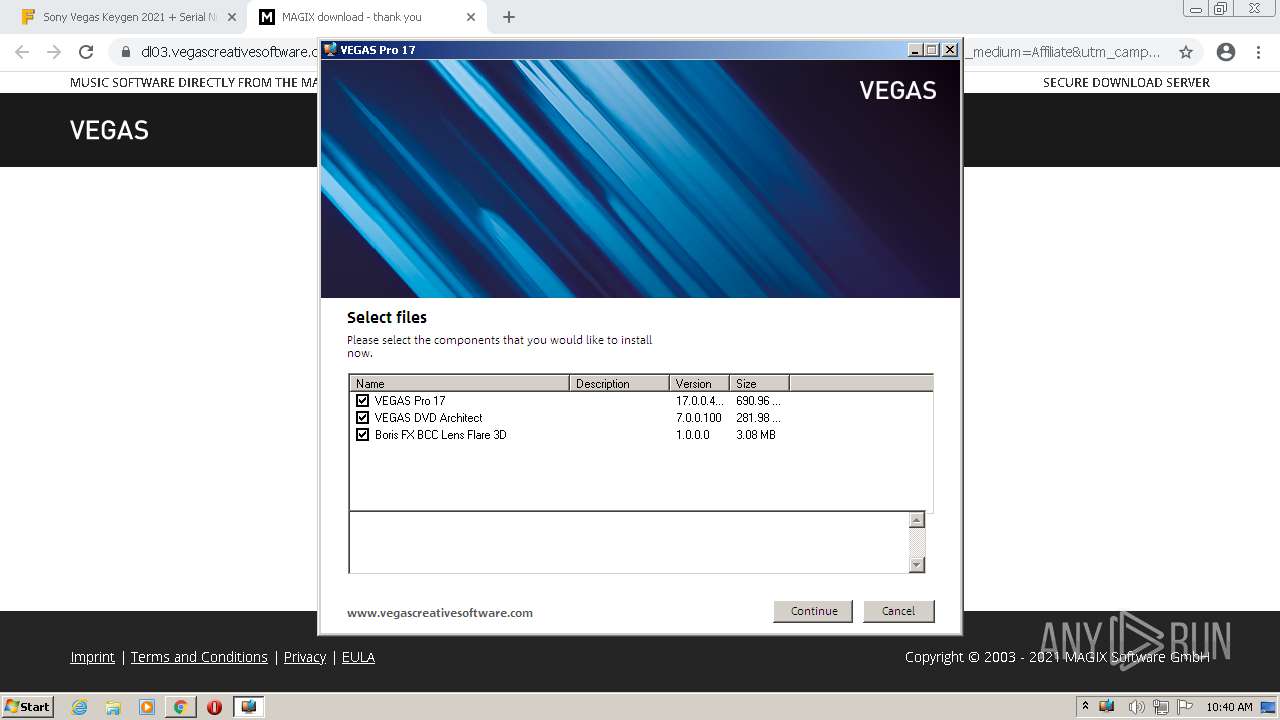
Application was dropped or rewritten from another process
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 3132)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 2924)
- MxDownloadManager.exe (PID: 2768)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 3944)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 3232)
- MxDownloadManager.exe (PID: 1556)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf (1).exe (PID: 3572)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf (1).exe (PID: 2776)
- MxDownloadManager.exe (PID: 1664)
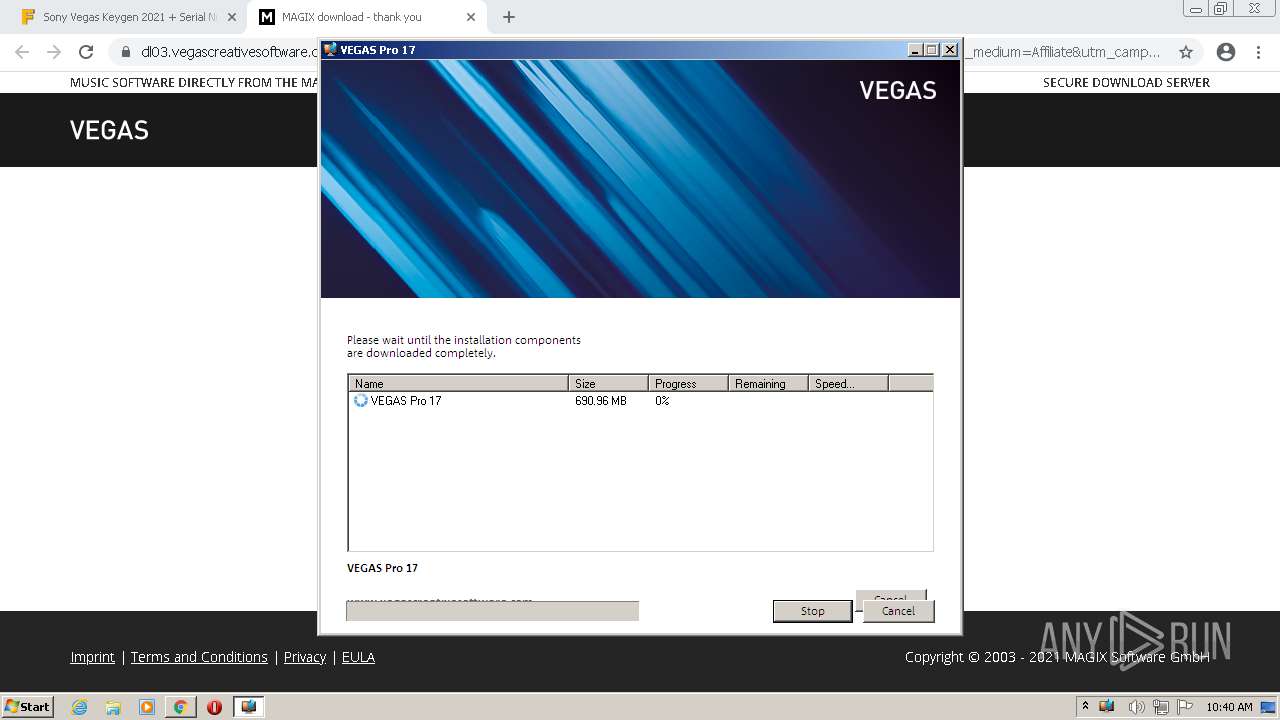
Drops executable file immediately after starts
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 2924)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 3944)
- chrome.exe (PID: 3912)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf (1).exe (PID: 3572)
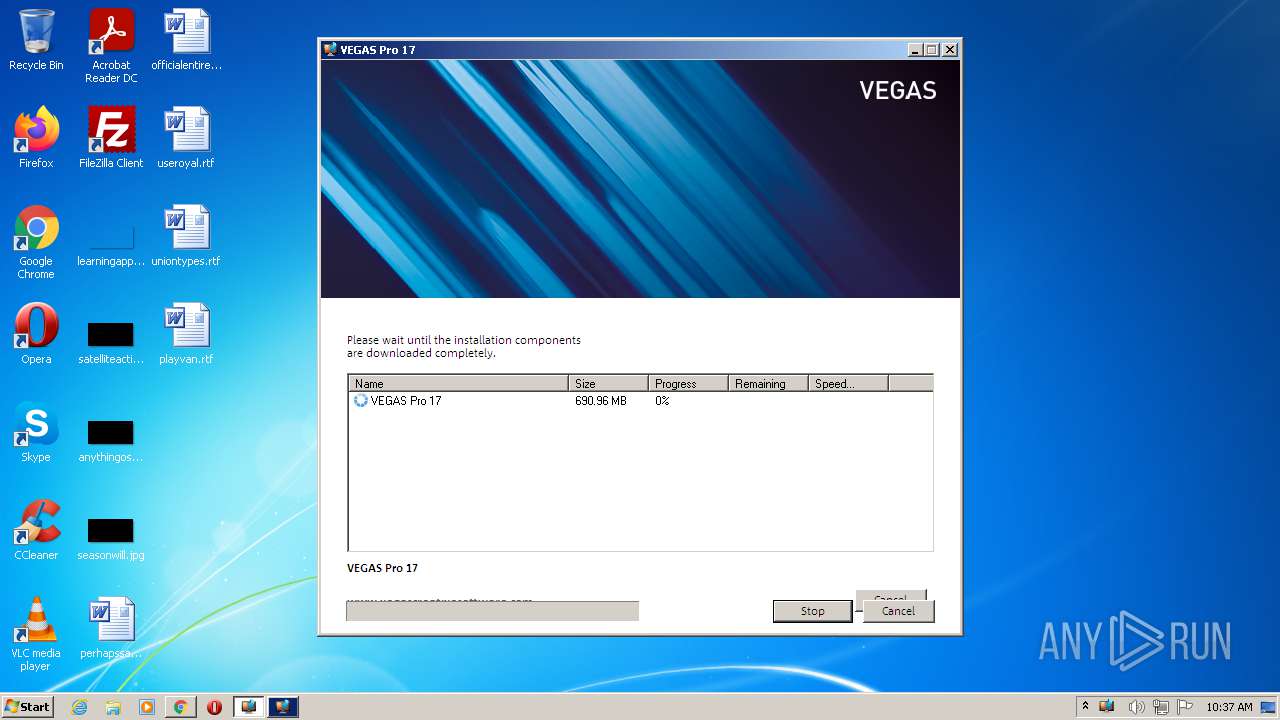
Loads dropped or rewritten executable
- MxDownloadManager.exe (PID: 2768)
- MxDownloadManager.exe (PID: 1556)
- MxDownloadManager.exe (PID: 1664)
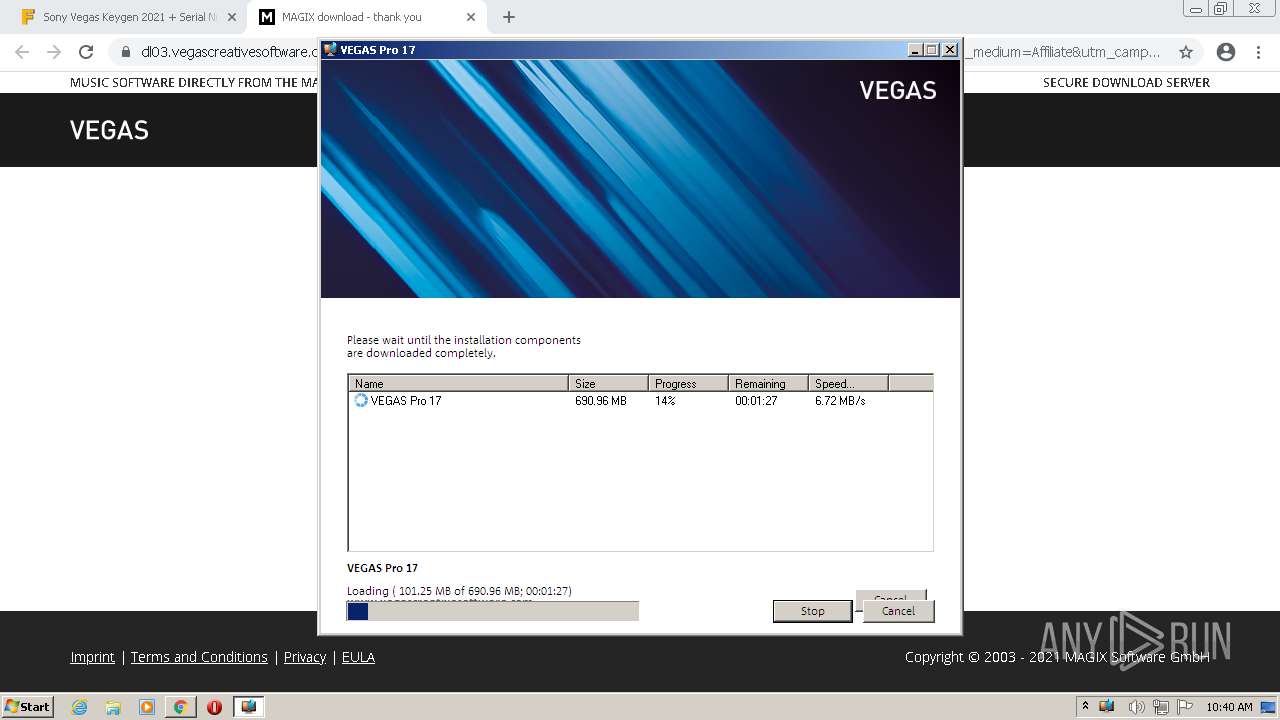
Changes settings of System certificates
- MxDownloadManager.exe (PID: 2768)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1200)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 2924)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 3944)
- chrome.exe (PID: 3912)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf (1).exe (PID: 3572)
Drops a file with a compile date too recent
- chrome.exe (PID: 1200)
Checks supported languages
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 2924)
- MxDownloadManager.exe (PID: 2768)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 3944)
- MxDownloadManager.exe (PID: 1556)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf (1).exe (PID: 3572)
- MxDownloadManager.exe (PID: 1664)
Reads the computer name
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 2924)
- MxDownloadManager.exe (PID: 2768)
- MxDownloadManager.exe (PID: 1556)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 3944)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf (1).exe (PID: 3572)
- MxDownloadManager.exe (PID: 1664)
Drops a file that was compiled in debug mode
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 2924)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 3944)
- chrome.exe (PID: 3912)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf (1).exe (PID: 3572)
Drops a file with too old compile date
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 2924)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf.exe (PID: 3944)
- trial_vegaspro17_dlm--phFL4Wje1syXqv4BCf (1).exe (PID: 3572)
Creates files in the user directory
- MxDownloadManager.exe (PID: 2768)
Adds / modifies Windows certificates
- MxDownloadManager.exe (PID: 2768)
INFO
Checks supported languages
- chrome.exe (PID: 1200)
- chrome.exe (PID: 2956)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 1628)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 1656)
- chrome.exe (PID: 2488)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 1044)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 612)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 2704)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 1924)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 1560)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 2484)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 2636)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 3912)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 864)
- chrome.exe (PID: 2584)
Reads the computer name
- chrome.exe (PID: 1628)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 1200)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 612)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 3872)
Reads settings of System Certificates
- chrome.exe (PID: 3616)
- chrome.exe (PID: 1200)
- MxDownloadManager.exe (PID: 2768)
- MxDownloadManager.exe (PID: 1556)
- MxDownloadManager.exe (PID: 1664)
Reads the hosts file
- chrome.exe (PID: 3616)
- chrome.exe (PID: 1200)
Application launched itself
- chrome.exe (PID: 1200)
Reads the date of Windows installation
- chrome.exe (PID: 612)
Checks Windows Trust Settings
- chrome.exe (PID: 1200)
- MxDownloadManager.exe (PID: 2768)
- MxDownloadManager.exe (PID: 1556)
- MxDownloadManager.exe (PID: 1664)
Creates files in the user directory
- chrome.exe (PID: 1200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
108
Monitored processes
57
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://fixthephoto.com/sony-vegas-keygen.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 | ||||
| 3060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6eb6d988,0x6eb6d998,0x6eb6d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 | ||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 3616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1036,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 | ||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 86.0.4240.198 | ||||
| 3964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 86.0.4240.198 | ||||
| 2956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 3532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1128 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 86.0.4240.198 | ||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1320 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,14570190004404730,3934894479344807684,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
39 867
Read events
39 388
Write events
0
Delete events
0
Modification events
Executable files
109
Suspicious files
54
Text files
263
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60FA8D90-4B0.pma | — | |
MD5:— | SHA256:— | |||
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\20a1f079-fdf6-492e-8cf6-67992de99221.tmp | text | |
MD5:80B7696214C5785B894BF501B0EB5CF8 | SHA256:D533A56DD05786E2DD21A0C8AAABD7719D97B84D485C4944F371439D132537DE | |||
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:80B7696214C5785B894BF501B0EB5CF8 | SHA256:D533A56DD05786E2DD21A0C8AAABD7719D97B84D485C4944F371439D132537DE | |||
| 3060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF2b372b.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF2b373b.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
96
TCP/UDP connections
142
DNS requests
104
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2768 | MxDownloadManager.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2768 | MxDownloadManager.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEAcrofrUV85obzSUznCt6iE%3D | US | der | 471 b | whitelisted |
2768 | MxDownloadManager.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEER7f5hIh7JG%2FggGnLYG2W0%3D | US | der | 471 b | whitelisted |
— | — | HEAD | 200 | 173.194.139.7:80 | http://r2---sn-aigzrn7k.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw?cms_redirect=yes&mh=LV&mip=185.217.117.45&mm=28&mn=sn-aigzrn7k&ms=nvh&mt=1627032739&mv=m&mvi=2&pl=26&rmhost=r1---sn-aigzrn7k.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
3616 | chrome.exe | GET | 200 | 72.21.91.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
— | — | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
— | — | HEAD | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
2768 | MxDownloadManager.exe | GET | 301 | 195.214.216.160:80 | http://www.magix.com/ | DE | html | 230 b | whitelisted |
2768 | MxDownloadManager.exe | GET | 301 | 195.214.216.160:80 | http://www.magix.com/ | DE | html | 230 b | whitelisted |
— | — | GET | 302 | 142.250.186.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 505 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3616 | chrome.exe | 142.250.185.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 142.250.181.226:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 185.59.220.198:443 | a.omappapi.com | Datacamp Limited | DE | suspicious |
3616 | chrome.exe | 143.204.98.109:443 | img.fixthephoto.com | — | US | suspicious |
3616 | chrome.exe | 216.58.212.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3616 | chrome.exe | 142.250.185.226:443 | googleads.g.doubleclick.net | Google Inc. | US | suspicious |
3616 | chrome.exe | 74.125.206.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3616 | chrome.exe | 216.58.212.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
fixthephoto.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
img.fixthephoto.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
z-na.amazon-adsystem.com |
| whitelisted |
a.omappapi.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
2768 | MxDownloadManager.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2768 | MxDownloadManager.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |